How PAC-MAN shows the importance of secure coding
At Nexor, we provide solutions to customers where security is critical. To meet our customers’ needs, it is essential to make sure the code we write meets basic security requirements, so that the end product can withstand various kinds of malicious attack.
It's all very complicated, and it's hard to explain to the non-technical crowd. Computers are complicated, and in a very strange and roundabout way, the problem with insecure code is that computers do exactly what you tell them to.
The problem with computers
Recently a colleague was trying to explain the basics of coding to a bunch of non-techies. He gave a very simple example of some insecure code – at least, simple to those who know the programming language C. For the layman it may be black magic.
For those not fluent in C programming, the key elements here are:
When this program is run, it asks for a bit of data from the user;
It puts that data in a box;
It then shows the contents of that box on the screen.
But there is a problem. The box is only so big, but the user can supply any amount of data.
Q: How do you get an elephant into a matchbox?
A: Take out all the matches first.
(Source: Every joke book for kids)
Tell a child to put a big thing in a small box and they'll look at you like you're strange and tell you the box is too small. Tell a computer "put this thing in that box" and it will.
It will do it regardless of the size of the box, and if the box is too small, it will break a hole in the bottom of it, then a hole through the floor, and then leave stuff all over the basement below.
Why? Because you told it to "put this thing in that box" instead of asking "fill this box up, but tell me if not all the stuff will fit in it".
How high can you count?
If you have any young children in your family, you will know that up to a certain age, kids will happily demonstrate how high they can count to. After a certain point, they get a bit confused. Computers are like this too.
If you ask a small child to keep counting after they've already gone as high as they can, they will probably tell you they can't. A computer however will do something rather bizarre.
In the real world, 255+1=256. But to a computer program, sometimes 255+1=0, or 0‑1=65535, or maybe 40,000+40,000=14464. – MITRE.
Essentially, when it doesn't know any more numbers, a computer will start again from the lowest number it knows.
The amount of numbers it knows depends on the amount of memory you tell the computer to use to remember a certain number. The lowest number the computer knows might be zero or it might be a very large negative number, depending on whether you tell it the number might be negative.
Computers make a distinction between these kinds of numbers, like temperatures or bank balances, and numbers that are always positive like sizes and counters.
So computers do funny things with numbers. Maybe a number a computer was counting resets to zero without you realising.
How is that a security issue?
Small bugs make big problems
The problem with computers is that a very small unexpected thing happening, like a number resetting to zero when you didn't expect it to, can have very big, very unexpected consequences.
To get a better idea of why, let's look at a real world example. It's not a security issue but it does show you the sorts of weird and wonderful things that happen just from a number resetting to zero.
Everyone knows the videogame PAC-MAN. You eat all the dots on the level while avoiding some ghosts, and then you move on to the next level and start again. Each level is basically the same but the ghosts get faster and the power-ups that help you last for less time. The game is supposed to go on for ever and never finish, until you run out of lives.
Unfortunately, the programmers told the computer that it only needed a small amount of memory to remember what level the player is on. So it can only count up to 255. When you reach level 256, that number resets to zero. So what happens? Does it just come up with "level 0" instead of "level 256"?
Nope – this happens:
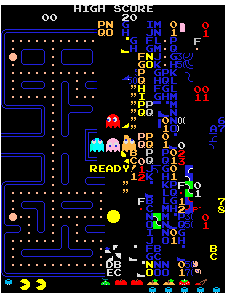
There are plenty of articles online that will explain exactly how this happens. The important point though is that such a seemingly small and irrelevant error has caused something very, very bad to happen.
If something so tiny and so trivial can do this to PAC-MAN, you need only imagine what could happen to a security critical system if an attacker deliberately tries to exploit similarly tiny errors.
Secure coding practice
Here at Nexor, we take the development our code above and beyond. A snapshot of some of the approaches that we incorporate into our CyberShield Secure® Software Development covers things such as:
Rigorous coding standards
Common libraries
Trusted suppliers
Static/dynamic analysis
Peer reviews
That’s why we were in the right place to be the first organisation in the world to achieve the TickITplus Software Quality Management certification scheme back in 2011 and more recently Nexor was a founding contributor to the PAS754 Trustworthy Software Standard.
So you see, PAC-MAN can show the importance of good secure code.
If you want to know more details about the PAC-MAN coding error, then check out the details on Wikipedia!
If you want to know more about secure code, then get in touch with us!

